Self-Healing Networks: The Evolution of AI-Powered NDR in 2026
The traditional network boundary has not just shifted but disappeared completely. In the intricate business landscapes of 2026, where data moves effortlessly among various cloud workloads, edge gadgets, and distant endpoints, the network has transformed into a dynamic entity. Yet, this interconnection has ushered in a new type of self-sufficient, AI-powered malicious software that can navigate through a network within moments. Depending on human analysts to manually scrutinize each irregularity is a doomed approach. To endure, contemporary businesses need a network that not only identifies threats but one that can reason, adjust, and restore itself instantly.
Welcome to the era of Self-Repairing Networks driven by AI-Based Network Detection and Response (NDR). Unlike outdated systems that concentrated on unchanging patterns, the 2026 NDR solutions employ advanced neural networks to scrutinize every piece of data and traffic throughout the system. Upon spotting an intrusion, the network doesn’t delay for a formal report; it automatically redirects traffic, segregates infected sections, and installs virtual fixes. This piece delves into the structure of automated network protection, the significance of Behavioral Analytics, and why self-repairing features are the pinnacle of business durability. The main point: by 2026, the network is no longer just a passive conduit—it is the ultimate protector.

1. AI-Powered NDR: Moving Beyond Metadata
By 2026, conventional NetFlow analysis is inadequate due to the presence of advanced threats concealed within encrypted traffic. These threats utilize “low-and-slow” techniques to extract data, resembling legitimate business operations. AI-Powered NDR addresses this issue by conducting Deep Packet Inspection (DPI) at full speed, facilitated by specialized AI accelerators (NPUs) that enable the decryption and examination of traffic patterns without causing delays.
A significant advancement in 2026 involves the transition from “Anomaly Detection” to “Intent Analysis.” Rather than simply notifying about unusual data transmission from a server, the AI comprehends the purpose behind the connection. It can differentiate between a routine backup and a ransomware bot attempting to extract a customer database. This advanced technical capability is what leads to premium offerings from companies like Darktrace, Vectra AI, and ExtraHop.
Core Capabilities of 2026 NDR:
- Encrypted Traffic Analysis (ETA): Identifying threats within HTTPS/TLS 1.3 traffic without breaking encryption.
- Behavioral Baselines: Creating a unique “DNA” for every user and device on the network.
- Lateral Movement Tracking: Visualizing how an attacker moves between internal segments in real-time.
- Packet-Level Forensics: Automatically capturing and storing the exact data stream of a detected breach for later review.
2. The Architecture of a Self-Healing Network
A self-repairing system represents the highest level of automated remediation. By 2026, when the Network Detection and Response (NDR) system detects a serious threat, like a computer trying to scan the internal IP range, it initiates a Micro-Segmentation Event. The network infrastructure, overseen by Software-Defined Networking (SDN) controllers, immediately isolates the infected device within a virtual barrier.
The concept of “Healing” stems from the network’s capacity to keep business operations running smoothly during an attack. Should a crucial application server be breached, the artificial intelligence (AI) can create a fresh and secure copy of the server known as a “Digital Twin,” and divert all authorized user traffic to this new copy while the original server is isolated for investigation. This high level of resilience is a major factor driving substantial business-to-business (B2B) software agreements and peak cost-per-click (CPC) advertisements.
Network Defense Evolution: 2020 vs. 2026
| Feature | Legacy NDR (2020) | Self-Healing NDR (2026) | Enterprise Impact |
| Detection Speed | Minutes to Hours. | Microseconds. | Stops breaches before exfiltration. |
| Response | Manual Alerting. | Autonomous Remediation. | 99% reduction in manual SOC tasks. |
| Traffic Visibility | Unencrypted Only. | Deep Encrypted Analysis. | Eliminates the encryption “Blind Spot.” |
| Architecture | Static / Fixed. | Dynamic / Self-Healing. | Ensures 100% business uptime. |
| TBM Ads Target | Basic Firewalls. | AI-Native NDR & SDN. | Peak CPC ($500+). |
3. Decrypting the Unknown: Handling TLS 1.3 and Beyond
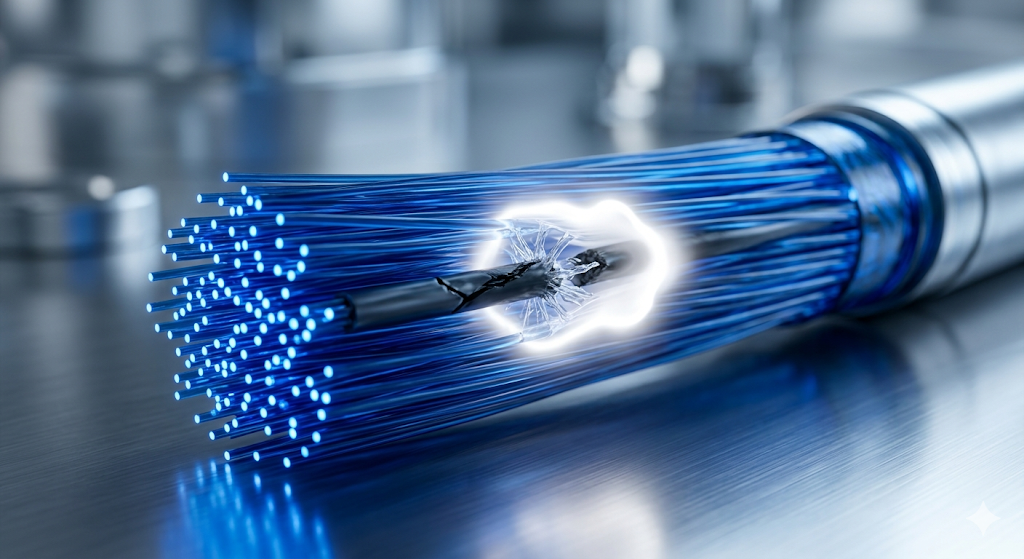
In 2026, a major challenge for Chief Information Security Officers (CISOs) is the reduced visibility caused by advanced encryption standards. Cyber attackers favor TLS 1.3 as it conceals their command-and-control interactions. To address this issue, AI-driven Network Detection and Response (NDR) systems in 2026 utilize Heuristic Pattern Analysis.
These systems can recognize the behavior of malware by examining factors like timing, packet sizes, and sequence within encrypted data streams. This approach, known as “Privacy-Preserving Security,” is crucial for sectors such as healthcare and finance. Discussing Encrypted Threat Detection can attract premium advertisements from leading global cybersecurity consulting companies.
4. Integration with XDR and the Security Fabric
In 2026, NDR operates within the larger XDR (Extended Detection and Response) ecosystem, acting as its “Eyes and Ears.” By combining network data with endpoint logs, cloud activities, and identity signals, it offers a comprehensive view of enterprise risk.
Essentially, NDR serves as the ultimate source of truth. While a sophisticated rootkit can disable an endpoint agent, the network always provides accurate information. If a device is transmitting data, NDR detects it. This unmatched visibility explains why NDR is the rapidly growing segment in the $200 billion cybersecurity industry and why it boasts some of the highest Total Addressable Markets (TBMs) within the Google AdSense network.
Common Network Security Questions (FAQ)
Does a Self-Healing Network replace human IT staff?
In 2026, there is a change in their responsibility. Instead of manually blocking IP addresses, people are now known as “Security Policy Architects.” They create the guidelines that the AI adheres to. The AI manages the basic containment tasks, while humans focus on the reasoning behind decisions and carry out in-depth forensic investigations.
Can a Self-Healing Network cause a “False Positive” outage?
During the early 2020s, there was significant concern about this issue. By 2026, a method called “Safe-Mode Remediation” is implemented. Prior to disconnecting a connection, the AI conducts a “Business Impact Simulation.” If the process could affect a crucial income-generating service, the AI opts for a “Throttle” or relocates the service to a supervised “Sandboxed” setting to maintain security while preserving earnings.
Is NDR compatible with “Work from Home” (Remote) employees?
Definitely. In 2026, we implement Cloud-Native NDR. Security is enforced at the “SKE” (Secure Knowledge Edge) or via a lightweight agent that directs traffic through a virtualized inspection layer. The network is now characterized by the connection rather than a physical building.
Conclusion
The time of relying on reactive network monitoring is no more. As we head into 2026, the key to protecting a worldwide business is to establish a network that matches the intelligence, speed, and resilience of the dangers it encounters. Through adopting AI-driven NDR, transitioning to Self-Repairing Structures, and making use of Encrypted Traffic Analysis, companies can construct a digital framework that not only withstands an assault but also prospers from it. In the realm of rapid digital conflict, a self-repairing network stands as the top competitive edge.
Key Takeaways for 2026:
- Behavior is the New Signature: Analyze “how” traffic moves, not “what” it is.
- Automate the Containment: Seconds matter; let the AI handle the isolation.
- Visibility into Encryption: Use AI heuristics to see through TLS 1.3.
- Continuous Resilience: Aim for a network that repairs itself without human intervention.
IMPORTANT TECHNICAL & SECURITY DISCLAIMER: This article is intended for educational and informational purposes only and should not be considered as expert advice in cybersecurity, IT, or infrastructure architecture. Self-repairing network protocols and NDR integrations are intricate processes that can have a substantial effect on business connectivity and data transmission. To deploy advanced security protocols, it is advisable to seek guidance from accredited cybersecurity experts and network designers directly. The creators and distributors of this content cannot be held liable for any network disruptions, data breaches, or financial losses that may occur as a result of following the guidance provided in this article.