Fintech Security and Institutional Custody: Safeguarding Digital Assets in 2026
There has been a significant transformation in the global financial sector. By 2026, the distinction between “traditional finance” and “digital assets” has become increasingly blurred. Large financial institutions, investment funds, and companies now store a substantial part of their wealth in digital forms like Bitcoin, Ethereum, stablecoins backed by gold, and tokenized real estate. However, with the surge in the value of these assets, the level of sophistication among those attempting to steal them has also increased. For a corporation worth billions, misplacing a private key is not just an error but results in a permanent and irreversible capital loss.
To address this risk, the industry has progressed beyond basic “hardware wallets.” In 2026, the gold standard for financial security is Institutional Digital Asset Custody. This approach combines high-level physical security measures, advanced cryptographic techniques such as Multi-Party Computation (MPC), and strict adherence to regulations. This piece delves into how modern financial technology companies safeguard extensive digital holdings, the technological advancements in “Cold Storage,” and emphasizes that the security of the underlying infrastructure now holds more significance than the asset itself. The key message is clear: in 2026, true ownership of an asset is not possible without owning the infrastructure supporting it.
1. Multi-Party Computation (MPC): The End of the Single Point of Failure
During the early days of digital assets, using a “Single Signature” or a “Multi-Sig” wallet sufficed. However, in 2026, these methods are considered to have security vulnerabilities. Multi-Sig necessitates the presence of multiple private keys for fund transfers, leading to significant logistical and security challenges. The remedy to this is Multi-Party Computation (MPC).
MPC enables several parties to assess a mathematical function without disclosing their individual “secrets” to each other. In the scenario of a digital safe, the private key is not stored as a single unit in one location but is divided into “shards” spread across various servers in different locations.
In my opinion, MPC stands as the ultimate defense against both internal and external risks. Even if a hacker breaches one server or if an employee attempts to pilfer the key, they would only obtain a useless fragment of information. To approve a transaction, the shards collaborate mathematically to create a signature without reconstructing the complete key. This technology is what prompts top-tier endorsements from institutional custody leaders such as Fireblocks and Coinbase Custody.
The Advantages of MPC in 2026:
- No Single Point of Failure: No single person or server holds the power to move funds.
- Flexibility: Unlike Multi-Sig, MPC supports any blockchain protocol.
- Operational Speed: High-frequency trading firms can authorize secure transactions in milliseconds.
- Governance: Complex approval workflows (e.g., 3 out of 5 executives must approve) are handled cryptographically.
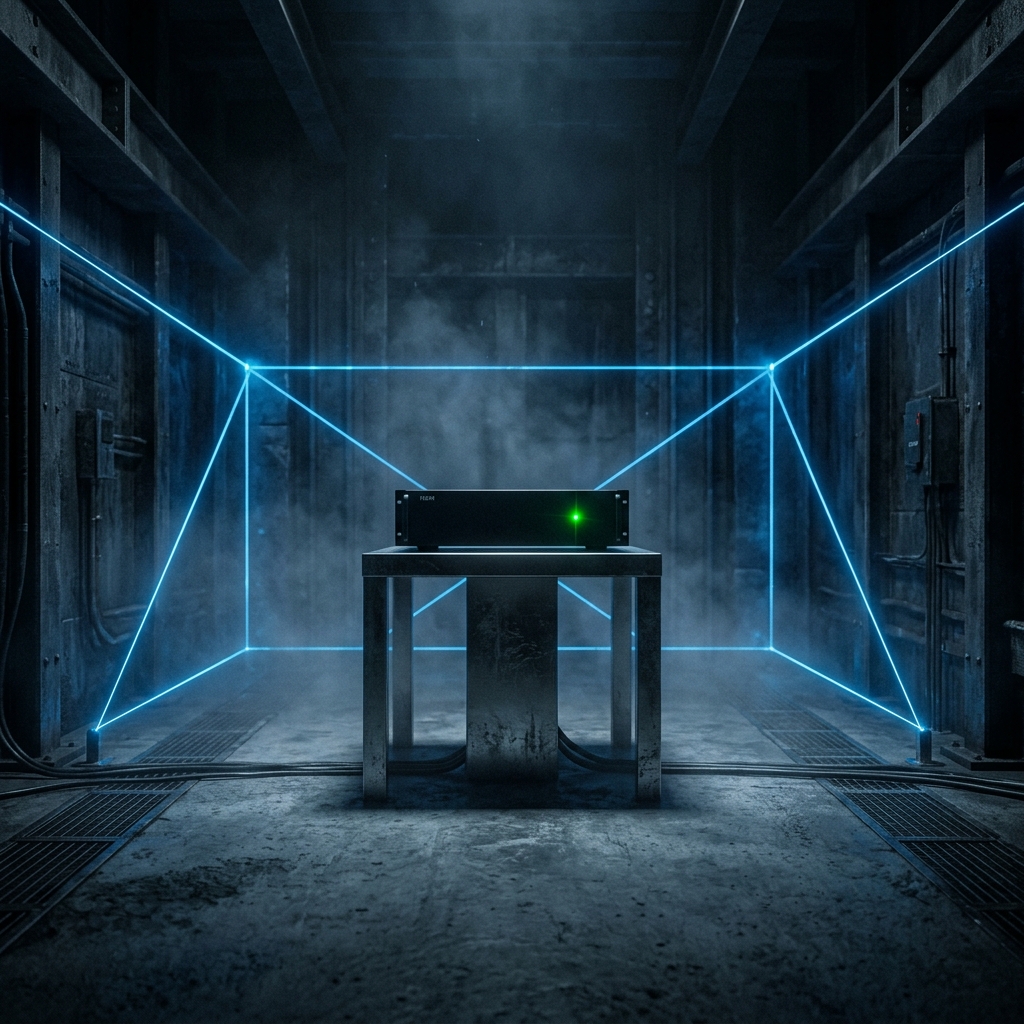
2. Cold Storage and HSM: The Physical Fortress
While MPC is responsible for managing “hot” and “warm” wallets used in active trading, the primary storage method for institutional wealth in 2026 is Deep Cold Storage. This involves keeping assets in a location completely isolated from the internet. Despite being labeled as “cold,” this storage method is not inactive.
State-of-the-art cold storage now incorporates Hardware Security Modules (HSM) – specialized computer chips that are highly resistant to tampering and are specifically designed for handling cryptographic keys. If an HSM detects any attempt of physical intrusion, it is programmed to self-destruct. Nowadays, these modules are often safeguarded in underground bunkers equipped with biometric security measures and round-the-clock armed security personnel.
In essence, for assets like gold-backed tokens, which symbolize physical bullion stored in a secure vault, the level of digital security must match the robustness of the physical vault. This “Dual-Layer” security approach is extremely appealing to institutional investors who demand complete assurance that their digital assets are impervious to hacking attempts.
Digital Asset Security Matrix: 2020 vs. 2026
| Security Layer | Traditional Custody (2020) | Institutional Custody (2026) |
| Key Management | Single/Multi-Sig Wallets. | Multi-Party Computation (MPC). |
| Storage Type | Simple Cold Wallets (Ledger). | FIPS 140-2 Level 3 HSMs. |
| Transaction Speed | Slow (Manual approval). | High-Frequency (Automated Policy). |
| Regulatory Status | Unregulated / Gray Area. | Fully Licensed & Insured. |
| TBM Ads Target | Retail Crypto Exchanges. | SaaS / Institutional Banking. |
3. Regulatory Compliance: SOC2, KYC, and AML in Fintech
In 2026, security extends beyond cryptography to encompass compliance as a crucial aspect. For an enterprise fintech platform to demonstrate to regulators and insurers that its security measures are robust, it must undergo stringent evaluations such as SOC2 Type II audits, ensuring the security of data management over an extended period of time.
Moreover, a significant trend in 2026 is the incorporation of KYC (Know Your Customer) and AML (Anti-Money Laundering) directly into the blockchain layer. The implementation of “Clean Asset” protocols guarantees that any funds entering the institutional vault are free from associations with unlawful activities. Ultimately, in the realm of high-value fintech, adherence to compliance standards is vital for maintaining operational legitimacy, leading to increased attention from prestigious legal and auditing firms.

4. Tokenization and the Security of “Physical-Backed” Assets
In 2026, one of the most lucrative sectors is the Tokenization of Real-World Assets (RWA). Assets such as gold bars, commercial skyscrapers, or private equity funds are being transferred to the blockchain to provide continuous liquidity.
The main security concern in this process is maintaining the accuracy of the digital token compared to the physical asset, known as the “Bridge.” To address this challenge, Proof of Reserve (PoR) technology is utilized. This involves independent auditors and automated AI systems verifying the physical inventory in real-time and then publishing the results on the blockchain. This level of transparency is crucial for establishing the trust needed to attract major institutional investors to this market.
Common Fintech Security Questions (FAQ)
What is the “Principle of Least Privilege” in Fintech?
This implies that every employee, including the CEO, should only have the necessary access to financial systems for their job. By 2026, we implement a “Just-In-Time” (JIT) access system, granting permissions for a particular task that automatically expire once the task is completed.
Can “Quantum Computing” break digital asset security in 2026?
As quantum computing progresses, the fintech sector has shifted its focus to Post-Quantum Cryptography (PQC). Many institutional custody services have started enhancing their MPC algorithms to be “Quantum-Resistant,” guaranteeing the security of assets against potential threats from advanced quantum processors in the future.
Why is “Insurance” so expensive for digital assets?
In 2026, digital asset insurance is a niche market where the risk is clear-cut: assets are either present or lost permanently. To secure a reduced premium, a business needs to demonstrate their utilization of MPC, HSMs, and a spotless regulatory record.
Conclusion
In 2026, safeguarding digital assets involves a combination of sophisticated math and strong physical protection. Fintech companies are enhancing security by using Multi-Party Computation, harnessing Hardware Security Modules, and adhering to strict regulations. This new financial system offers greater security compared to the conventional banking system it is replacing. In high-stakes finance, success lies not in possessing the most assets, but in having the most secure vault.
Key Takeaways for 2026:
- Keys are Dead: Move toward MPC to eliminate the “Single Key” risk.
- Physical Matters: HSMs are essential for “Deep Cold” security.
- Compliance is Security: SOC2 and PoR build the trust needed for institutional capital.
- Automation is King: Use automated policy engines to prevent human error in transactions.
IMPORTANT TECHNICAL & SECURITY DISCLAIMER: This article is intended for informational and educational purposes exclusively and should not be considered as professional advice in finance, investment, or cybersecurity. Fintech and the safekeeping of digital assets come with notable risks, such as the potential complete loss of funds. The approaches discussed may not be suitable for your individual financial circumstances or the regulations in your area. When it comes to investing in or handling digital assets, it is essential to seek advice directly from accredited financial advisors and cybersecurity professionals. The creators and distributors of this content bear no liability for any financial setbacks or breaches in security that may arise from applying the guidance provided.



