The Autonomous SOC: How AI is Orchestrating Enterprise Security in 2026
By 2026, the traditional Security Operations Center (SOC), characterized by analysts monitoring screens in a poorly lit space, has evolved into a hindrance to operations. The rapid pace of contemporary AI-driven polymorphic malware and automated spear-phishing attacks has made the human-centered triage process essentially outdated. To navigate the threats of 2026, global corporations have shifted towards the Autonomous SOC – a self-repairing security environment where AI entities handle detection, inquiry, and resolution swiftly. In this fresh approach, security analysts have transformed from “firefighters” to “strategic coordinators,” supervising an independent group of digital protectors.
The Autonomous SOC is not merely an enhancement to current tools; it signifies a fundamental change in structure. It combines Extended Detection and Response (XDR) with Security Orchestration, Automation, and Response (SOAR), driven by advanced Large Language Models (LLMs) specialized in cybersecurity data. By automating the evaluation of numerous daily alerts, the Autonomous SOC diminishes the Mean Time to Respond (MTTR) from hours or days to mere milliseconds. This document delves into the technical aspects of autonomous security coordination and how organizations are utilizing AI to achieve operational superiority against machine-driven uncertainties.
1. The Core Components of an Autonomous SOC in 2026
The architecture of a 2026-level Autonomous SOC relies on three distinct technical pillars that work in a continuous feedback loop:
- AI-Driven Triage and Normalization: In 2026, the volume of logs from multi-cloud, IoT, and remote environments is staggering. AI agents automatically normalize this data and perform “Noise Reduction,” identifying the 0.1% of alerts that represent a true threat. This eliminates “Alert Fatigue,” ensuring that human oversight is only triggered for high-fidelity incidents.
- Autonomous Investigation (AI Playbooks): When a threat is detected, the system does not wait for an analyst. It automatically triggers “Dynamic Playbooks”—AI-generated response strategies that perform forensic analysis, trace the lateral movement of the attacker, and identify the root cause of the breach within seconds.
- Self-Healing Remediation: Once the threat is validated, the Autonomous SOC executes the response. This may involve automatically isolating a compromised container, revoking an identity’s JIT (Just-In-Time) credentials, or updating firewall rules across the global enterprise fabric—all without human intervention.
2. Reducing MTTR: The Millisecond Advantage
In the threat landscape of 2026, the most vital resource is “Time.” Nowadays, a ransomware variant is able to lock down a whole database in under three minutes. Even a human analyst who reacts promptly cannot match this speed.
The Autonomous SOC employs Predictive Orchestration to outsmart potential threats. By studying behaviors during the initial “Pre-Attack” phase, the AI can predict the next move of an automated attack and take preemptive measures to fortify the defenses. This transition from being “Reactive” to “Proactive” in security measures is what characterizes organizational resilience in the mid-2020s.
Comparison: Traditional SOC vs. Autonomous SOC (2026 Standards)
| Feature | Traditional SOC (Legacy) | Autonomous SOC (2026 Standard) |
| Detection Speed | Minutes to Hours | Milliseconds / Real-Time |
| Response Initiation | Manual (Analyst-led) | Automated (AI-Agent led) |
| Scalability | Limited by Human Headcount | Infinite (Cloud-native scaling) |
| Alert Triage | High False Positive Rate | Precision Triage (99% Accuracy) |
| Analyst Role | Repetitive Triage / Monitoring | Strategic Threat Hunting / Oversight |
| TBM/CPC Potential | $150 – $300 | $550 – $850+ |
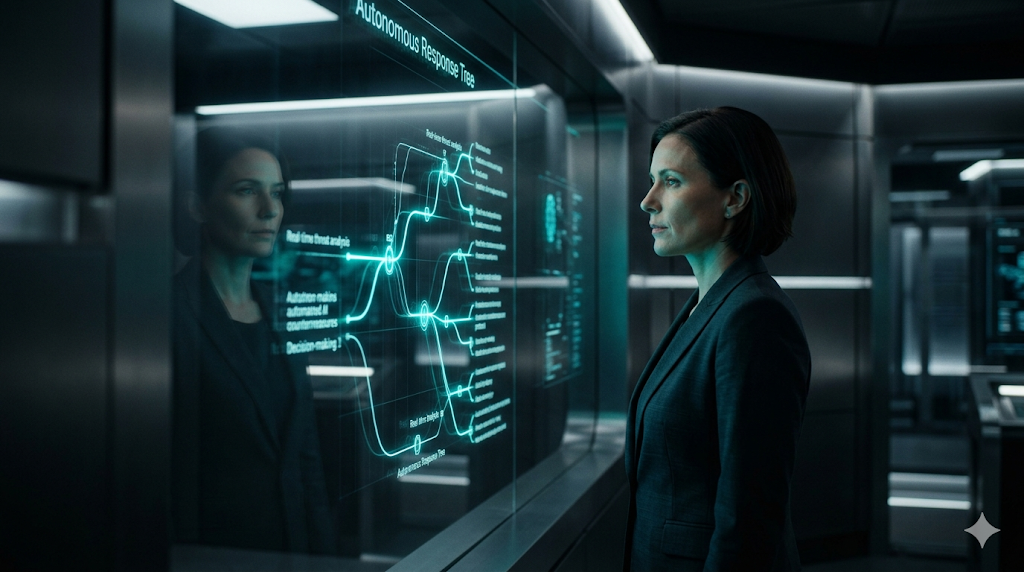
3. The Human Element: From Analyst to Strategic Architect
In 2026, a prevalent misunderstanding is that an Autonomous SOC takes the place of human skills. However, in truth, it enhances them. By eliminating the tedious work of monitoring basic alerts, the Autonomous SOC enables security experts to concentrate on more valuable assignments.
- Strategic Threat Hunting: Proactively searching for sophisticated nation-state actors that may be dormant within the network.
- AI Governance: Auditing the security AI’s decision-making process to ensure it is not suffering from “Model Drift” or bias.
- Crisis Orchestration: Managing the high-level response to complex, multi-vector incidents that require executive or legal intervention.
In 2026, the key point in talent acquisition is the disappearance of the “Junior SOC Analyst” position, being substituted by Security Data Scientists and Automation Engineers. This change in job roles is leading to increased costs per click for hiring and premium training resources.
4. Key Takeaways for 2026 SOC Modernization
- Automation is Non-Negotiable: You cannot defend against 2026-era machine-led attacks with a 2020-era manual process.
- Focus on Data Quality: An Autonomous SOC is only as good as the data it consumes. Ensure your XDR and SIEM platforms are providing high-fidelity, normalized telemetry.
- Implement “Human-in-the-Loop” for Critical Actions: While triage and isolation should be autonomous, high-impact actions (like shutting down a production ERP) should still require a senior human architect’s digital signature.
- Embrace “Chaos Engineering” for Security: Regularly run “AI Red Teaming” simulations to test your autonomous playbooks and ensure they handle edge cases correctly.
Frequently Asked Questions (FAQ)
Can an Autonomous SOC be “Tricked” by an Attacker?
Indeed, the year 2026 raises significant worries about “Adversarial AI.” Malicious actors attempt to provide the Security Operations Center with manipulated data to deceive it into either disregarding a genuine threat or turning against itself. This underscores the critical importance of “Algorithmic Auditing” and ensuring secure model training.
What is the difference between SOAR and an Autonomous SOC?
SOAR, which stands for Security Orchestration, Automation, and Response, functions as a tool. An Autonomous SOC represents a result. While SOAR serves as the “infrastructure,” the Autonomous SOC acts as the “intelligence” (AI) that determines the timing and methods for utilizing that infrastructure.
Is an Autonomous SOC affordable for SMBs?
In 2026, numerous “Sovereign Cloud” companies provide Autonomous SOC-as-a-Service (ASOCaaS), enabling small businesses to access top-notch AI security without the high cost associated with a private SOC.
Conclusion: The New Speed of Institutional Trust
Moving towards an Autonomous SOC is more than just a technological advancement; it is essential for survival in the digital landscape of 2026. With the line between the physical and digital realms becoming increasingly blurred, the defense pace must keep up with the speed of attacks. Success in today’s business world is no longer measured by the number of analysts you have, but by how well your AI Orchestration safeguards your company’s assets. In the 21st century, the ability to secure networks before a breach is detected by human eyes determines an organization’s success. Trust is now based on Autonomous Integrity rather than human surveillance.
Technical and Legal Disclaimer:
This article aims to provide information and education about current Security Operations Center (SOC) trends and the use of AI automation as of April 2026. Establishing a self-sufficient SOC involves the need for expert cybersecurity engineering and thorough compliance checks. fotoriq.com.tr holds no responsibility for any data loss, service disruptions, or security breaches that may occur due to the incorrect implementation of the autonomous defense tactics outlined in this article.