CIAM in 2026: Balancing Enterprise Security and Seamless Customer Experience
In the highly competitive digital landscape of 2026, the login page serves as the modern gateway to your brand. However, large corporations are confronted with a challenging dilemma: customers insist on maximum protection for their information, yet they have no patience for any obstacles related to security. Should a multi-factor authentication (MFA) procedure take too long or seem cumbersome, customers will abandon their shopping carts and opt for a rival’s services. This situation has transformed Customer Identity and Access Management (CIAM) from a basic “login box” into a vital “Trust Platform.” In the year 2026, CIAM plays a crucial role in delivering personalized interactions while safeguarding millions of users from identity theft and account takeover (ATO) incidents.
In contrast to internal Workforce IAM, which emphasizes control and limitations, CIAM prioritizes Scalability and User Experience (UX). It needs to manage numerous simultaneous logins, link with marketing systems, and adhere to international data protection regulations—all without being noticeable to the end-user. This piece delves into the structure of contemporary CIAM, the emergence of Progressive Profiling, and the significance of “Invisible Security” as the key competitive edge for enterprises in 2026. The main message is clear: if your security is conspicuous in 2026, it is not effective.

1. The Core of CIAM: Security Without Friction
In 2026, the preferred method for CIAM is Adaptive (Risk-Based) Authentication. Instead of making all users go through a complicated MFA process each time they log in, the CIAM platform utilizes AI to assess numerous indicators in the background. It evaluates the health of the user’s device, their location, their typing patterns (behavioral biometrics), and even the reputation of their IP address.
When the AI determines that the risk is minimal, users are granted a “Seamless Login” (often without a password through Passkeys). Only in scenarios where the risk is elevated—like logging in from a new device or carrying out a high-value transaction—does the system require a biometric verification through a “Step-Up” process. This level of intelligence is what prompts top-tier B2B advertisements from providers such as Okta (Auth0) and Ping Identity.
The Pillars of a 2026 CIAM Strategy:
- Scalability: The ability to handle sudden spikes (e.g., Black Friday) with zero latency.
- Omnichannel Identity: A single identity that follows the customer across mobile apps, web, and physical stores.
- Privacy-by-Design: Built-in consent management for GDPR, CCPA, and the new AI Privacy Acts.
- Social & Enterprise Login: Allowing users to log in with Google, Apple, or corporate IDs (SSO) seamlessly.
2. Progressive Profiling: Building Trust, One Click at a Time
Based on my experience as a developer and strategist, I have found that nothing hampers conversion rates more than a lengthy registration form with 20 fields. In the year 2026, advanced CIAM platforms utilize Progressive Profiling as a solution. Instead of requesting all information at once, the system initially only requires a name and email address during the first interaction. As the customer engages more with the brand over time, the system gradually prompts for additional information, such as preferences or location, at the “point of value.”
Essentially, progressive profiling transforms the concept of “Security” into “Personalization.” By the time users complete their full profiles, they have already established trust in the platform. This data-centric strategy is a key focus for high-CPC advertisements by Salesforce and Adobe, aiming to merge CIAM data into their marketing platforms.
IAM vs. CIAM: The Strategic Difference (2026)
| Feature | Workforce IAM (Internal) | Enterprise CIAM (External) |
| Primary Goal | Risk Mitigation / Control. | Revenue Growth / UX / Trust. |
| User Volume | Thousands (Employees). | Millions (Customers). |
| User Experience | Managed Friction. | Zero-Friction (Invisible). |
| Privacy Focus | Internal Policy. | Global Compliance (GDPR/CCPA). |
| TBM Ads Target | Security Hardware. | SaaS Identity & Marketing Tech. |
3. The End of the Password: Passkeys in the B2C World
By 2026, passwords are considered outdated, with Passkeys (FIDO2) now being the required standard for CIAM. Passkeys enable users to authenticate using their phone’s facial recognition or fingerprint, which is securely linked to the specific website. This innovation tackles the issue of forgotten passwords, which is responsible for 40% of help-desk expenses and many abandoned login attempts.
In essence, Passkeys offer a secure shield against phishing attacks. Even if a user falls for a fraudulent site, their Passkey won’t function there as it is uniquely tied to the authentic domain. This concept of an “Unbreakable Identity” is a key concept in premium B2B campaigns aimed at the retail and tourism industries.
4. Consent Management and the “Data Privacy” ROI
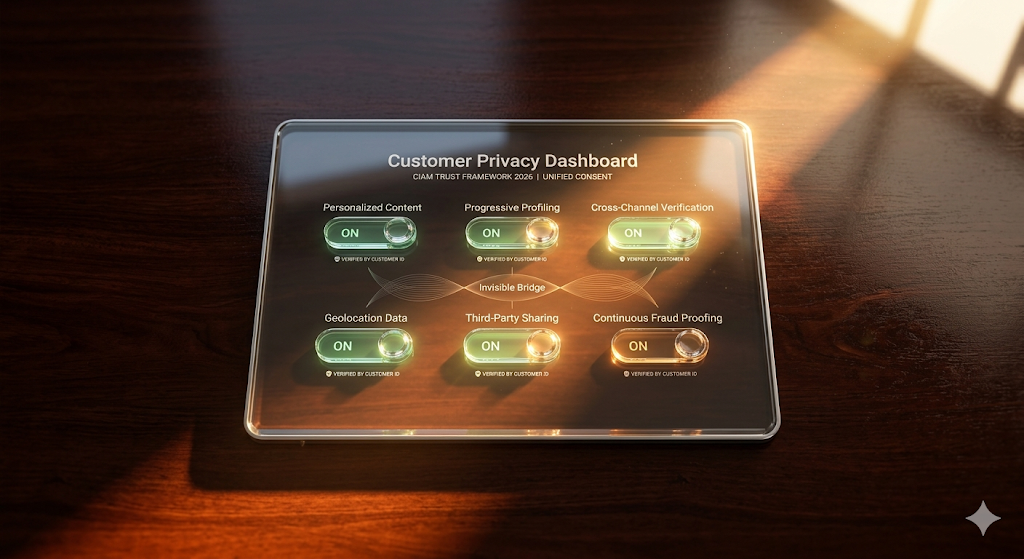
By 2026, privacy has become a key component of product offerings. A modern CIAM platform serves as the primary source for Consent management, ensuring that when a customer updates their marketing preferences or exercises their Right to be Forgotten, this information is synchronized across all enterprise systems like CRM, Marketing, and ERP.
In my personal experience, this automated compliance mechanism is essential to steer clear of the hefty fines prevalent in 2026. It also fosters “Brand Integrity.” By providing customers with a transparent “Self-Service Portal” for managing their data, they feel empowered and more loyal to the brand. This “Trust Equity” serves as a compelling argument for executives and is a crucial factor in attracting high-value GRC and Legal investments.
Common CIAM & Identity Questions (FAQ)
How does CIAM help prevent “Account Takeover” (ATO)?
In 2026, CIAM platforms are equipped with Credential Stuffing Protection. They analyze each login try by cross-referencing it with a vast database of compromised credentials from various breaches. Upon detecting a match, the system triggers a password reset and notifies the security team, effectively halting the attack proactively.
Can we use CIAM to comply with the “Right to be Forgotten”?
Certainly. By 2026, CIAM platforms will incorporate workflows for “Identity Orchestration”. Through a single user click, the CIAM system can issue a “Delete Command” to all databases and third-party SaaS tools containing the user’s data, while also maintaining a comprehensive record of the deletion process.
Is CIAM only for big retailers?
In 2026, B2B SaaS companies also utilize CIAM for managing their business customers (B2B2C). This enables them to provide “Self-Service Administration” to clients, empowering them to handle their employees’ access independently without needing to contact support.
Conclusion
In 2026, CIAM plays a crucial role in driving the digital economy forward. Transitioning from a restrictive “Gatekeeper” approach to a more empowering “Trust Enabler” strategy allows companies to provide customers with the smooth experiences they desire, all while meeting the high security standards of the times. By utilizing Adaptive Authentication, Progressive Profiling, and embracing Passkeys extensively, you can transform your identity framework into a potent marketing asset. In the 2026 landscape, identity serves as a connection rather than a hindrance between your business and its customers.
Key Takeaways for 2026:
- Invisible is Better: Aim for a zero-friction login experience for low-risk users.
- Personalize through Trust: Use progressive profiling to gather data as the relationship grows.
- Kill the Password: Adopt FIDO2 Passkeys to eliminate phishing and forgotten passwords.
- Centralize Consent: Make your CIAM the “single source of truth” for all privacy preferences.
IMPORTANT TECHNICAL & SECURITY DISCLAIMER: This article serves as an informative and educational resource only and does not serve as professional advice in cybersecurity, IT, or identity management. Scaling the implementation of Customer Identity and Access Management (CIAM) involves intricate architectural decisions and integration with external marketing and data systems. Each business environment is distinct, and the strategies discussed may not be suitable for your specific user base or local privacy laws such as GDPR, CCPA, BIPA. To implement advanced CIAM procedures, it is advisable to seek guidance from certified identity architects and data privacy experts. The authors and publishers hold no liability for any security breaches, data loss, or financial harm that may occur as a result of using the information provided in this article.



