Cyber Vaulting and Air-Gapped Resilience: The Final Frontier of Ransomware Defense in 2026
In the rapidly changing world of cybersecurity in 2026, the traditional method of backing up data, once a reliable safety measure, is now a prime target for advanced ransomware attacks driven by machines. Rather than simply encrypting main data sources, cybercriminals now spend considerable time infiltrating networks to locate and infiltrate online backup systems, leaving victims with little choice but to meet their demands. This new trend, known as “Backup-Seeking,” has led to a shift in focus towards Cyber Vaulting and Air-Gapped Resilience strategies. For large corporations, the goal is no longer just to have backups but to possess an “Isolated Record of Truth” that is physically or logically separated from the primary network infrastructure.
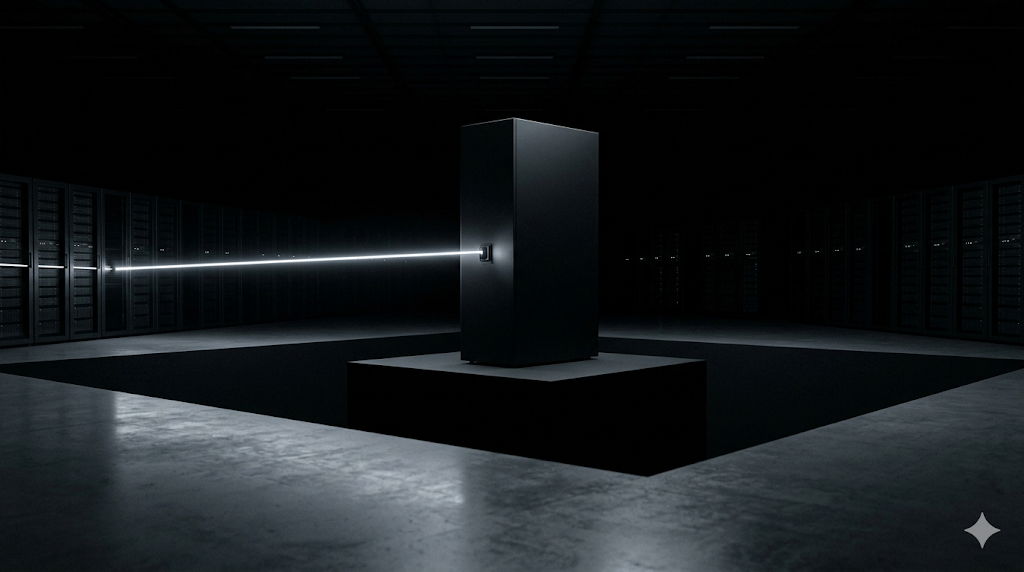
A Cyber Vault is a secure, isolated environment designed to safeguard an organization’s most crucial data in an unchangeable, air-gapped condition. In 2026, this is accomplished through a mix of physical isolation, closely monitored “Cleaning Channels,” and automated integrity verifications. By keeping an original copy of data shielded by a managed air-gap, organizations can guarantee that even if the primary system and cloud backups are compromised, the essential business data can be restored from a clean source. This manual delves into the technical setup of cyber vaulting in 2026 and how companies are employing “Isolation as a Defense” to navigate the ransomware-dominated landscape.

1. The Architecture of Isolation: Physical vs. Logical Air-Gaps
The effectiveness of a 2026-level cyber vault depends on the integrity of the Air-Gap. There are two primary technical implementations:
- Physical Air-Gap: The data is stored on offline media (such as high-density robotic tape libraries or specialized 2026-era optical storage) that is physically disconnected from the network. While this provides the highest level of security, it offers the slowest recovery time.
- Logical Air-Gap (The Digital Moat): The vault exists on-premises or in a specialized “Sovereign Cloud” environment. The connection between the production network and the vault is only opened for a brief window to transfer data. Once the transfer is complete, the connection is “severed” at the protocol level, and the vault returns to a “Dark” state, invisible to the rest of the enterprise.
2. Technical Pillars: Immutability and Automated Scrubbing
In 2026, a cyber vault is more than just a place to store data passively; it functions as a proactive and protective environment. It is supported by three indispensable foundations:
- Data Immutability (WORM): Once data enters the vault, it is locked using Write-Once-Read-Many (WORM) technology. Even an administrator with “Keys to the Kingdom” credentials cannot delete or modify the data until the pre-defined retention period expires.
- Automated Data Scrubbing: Before data is committed to the vault, it passes through a “Cleaning Zone.” In 2026, AI agents scan the incoming stream for hidden ransomware triggers, suspicious encryption patterns, or “logic bombs” that may be lying dormant.
- Vault Analytics: The vault continuously performs “Integrity Audits.” If the AI detects that the data being sent to the vault is significantly different from the previous day’s data (e.g., a massive sudden entropy change indicative of encryption), it triggers an immediate lockdown and alerts the SOC.
Comparison: Standard Cloud Backup vs. Cyber Vaulting (2026)
| Feature | Standard Cloud Backup | 2026 Cyber Vault Architecture |
| Connectivity | Always-On / Online | Air-Gapped / Disconnected |
| Data Integrity | Standard Checksum | AI-Driven Integrity Scrubbing |
| Access Control | IAM / RBAC | Multi-Factor Quorum (Physical/Digital) |
| Visibility | Part of Network Fabric | Hidden / Isolated Environment |
| Recovery Role | Operational Failover | The “Last Resort” Survival Record |
| TBM/CPC Potential | $200 – $350 | $450 – $750+ |
3. The Recovery Orchestration: Rebuilding from the Vault
In 2026, the most critical assessment for a cyber vault is the Recovery Orchestration. Due to the vault’s isolation, it is crucial to carefully control the process of reintroducing the data into a “Clean” production environment to prevent re-infection.
- Clean Room Recovery: In 2026, enterprises maintain “Isolated Recovery Environments” (IRE). The data is restored from the vault into this sterile IRE, where it is thoroughly tested and verified by an Autonomous SOC before being pushed back to the live network.
- Priority-Based Restoration: 2026-level orchestration software identifies the “Minimum Viable Business” (MVB) data. It ensures that the most critical systems (e.g., the financial ledger or identity database) are restored first, allowing the enterprise to function while the rest of the multi-petabyte data store is gradually recovered.
4. Key Takeaways for 2026 Resilience Strategy
- Assume the Breach: Design your resilience strategy with the assumption that your primary backups will be targeted and encrypted.
- Define Your MVB: Identify the absolute minimum data required for your institution to survive. This is what goes into the Cyber Vault.
- Audit the “Opening” Window: The moment the air-gap is bridged to transfer data is the moment of highest risk. Use AI-driven monitoring to ensure no lateral movement occurs during this window.
- Enforce a Quorum: No single human or machine identity should have the power to unlock the vault. Require a “Digital Quorum” from at least three distinct business units to authorize a recovery event.
Frequently Asked Questions (FAQ)
Does a Cyber Vault replace my DR site?
A Disaster Recovery (DR) site is designed for ensuring high availability and quick response, while a Cyber Vault is essential for ensuring survival. In the event of ransomware infecting your DR site, the Cyber Vault becomes the sole solution for data recovery.
Is Cyber Vaulting only for large banks?
In 2026, the response is negative. Thanks to the emergence of Cyber Vault-as-a-Service (CVaaS), medium-sized businesses are now employing separate storage levels to safeguard their valuable information and client data from the massive ransomware industry worth $30 trillion.
How often should data be sent to the vault?
The frequency of data backups relies on your Recovery Point Objective (RPO). By 2026, many organizations are opting for a “Differential Sync” every 4 to 24 hours to the secure vault, finding a balance between minimizing data loss and ensuring data isolation.
Conclusion: The Architecture of Perpetual Integrity
In the evolving digital environment of 2026, where cyber assaults orchestrated by machines can swiftly breach traditional boundaries, the most effective form of protection is Isolation. Cyber Vaulting stands as the ultimate defense against ransomware, offering a secure haven for data that remains shielded from the disruptions of the interconnected world. The concept of accountability in 2026 revolves around the understanding that while halting attacks may not always be possible, enduring them is imperative. Through the implementation of isolated resilience, global organizations are not merely storing information but are also safeguarding the core “Digital DNA” of their operations. Trust is now established not by the strength of barriers, but by the unwavering integrity of the secure vault itself.
Technical and Legal Disclaimer:
This article is meant to provide information and education on cybersecurity and data resilience trends as of April 2026. Creating and setting up a Cyber Vault necessitates specific engineering skills and thorough security assessments. fotoriq.com.tr is not responsible for any data loss, unsuccessful recovery, or ransomware attacks that may occur due to incorrect use of the isolation methods mentioned in this article.